DarkGate is malicious software that can steal sensitive data, perform cryptocurrency mining, and download additional payloads on infected systems. It has been observed to spread through compromised Skype accounts, posing as legitimate messages with PDF attachments. In this article, we will explore how DarkGate works, how it infects Skype users, and how to protect yourself from this threat.
Contents
How DarkGate Works
DarkGate is a commodity loader that was first documented in late 2017. It has various features that allow it to perform the following actions:
- Execute discovery commands (such as directory traversal)
- Self-update and self-manage
- Implement remote access software (such as remote desktop protocol or RDP, hidden virtual network computing or hVNC, and AnyDesk)
- Enable cryptocurrency mining functionality (start, stop, and configure)
- Perform keylogging
- Steal information from browsers
- Privilege escalation
DarkGate uses a Windows-specific automation and scripting tool called AutoIt to deliver and execute its malicious capabilities. AutoIt is a legitimate tool that can be used to automate tasks and create graphical user interfaces. However, it has been frequently abused by malware authors for defence evasion and an added obfuscation layer.
Check out some of the most recent trending articles:
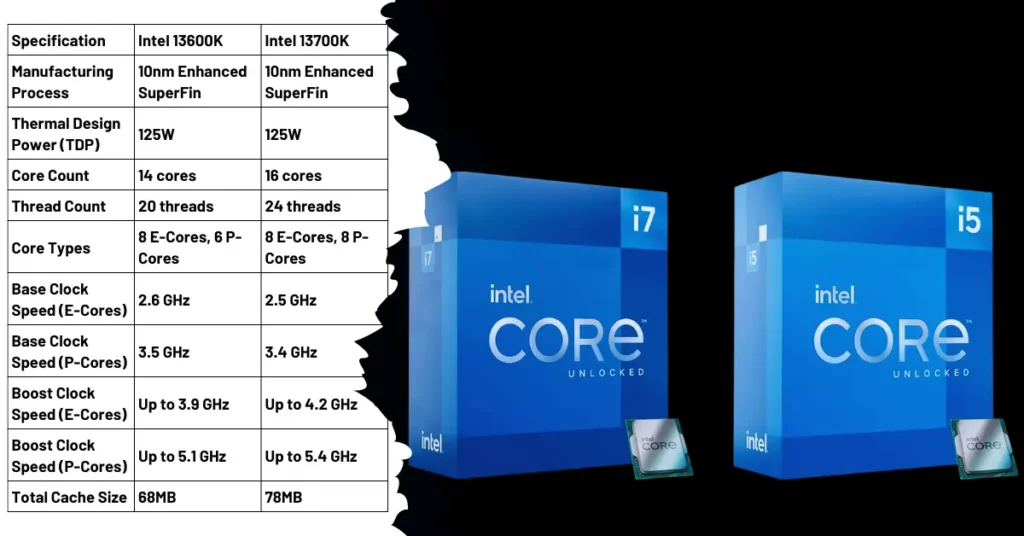
- Intel Launches 14th-Gen Raptor Lake Refresh: Faster Gaming and Multitasking Performance
- Reaction Effects in FaceTime: How to Make Your Video Calls More Fun and Expressive
How DarkGate Infects Skype Users
DarkGate attacks have used compromised Skype accounts to infect targets through messages containing VBA loader script attachments. VBA stands for Visual Basic for Applications, a programming language that can be embedded in Microsoft Office documents.
The VBA script masquerades as a PDF document, which, when opened, triggers the download and execution of an AutoIt script designed to launch the DarkGate malware. The attackers are able to hijack existing Skype messaging threads and craft the naming convention of the files to relate to the context of the chat history.
Bleeping Computer shared a post on Twitter:
DarkGate malware spreads through compromised Skype accounts – @sergheihttps://t.co/9135qNydnVhttps://t.co/9135qNydnV
— BleepingComputer (@BleepinComputer) October 14, 2023
This makes the messages appear more convincing and increases the likelihood of the recipients opening the attachments. For example, if the chat history is about a project report, the attachment may be named “Project Report.pdf” or something similar.
The infection chain of DarkGate abusing Skype is shown in Figure 1.
Figure 1: DarkGate infection chain via Skype
How to Protect Yourself from DarkGate
To prevent DarkGate infection via Skype, users should follow these best practices:
- Do not open or download any suspicious attachments from unknown or unexpected senders, even if they appear to be from your contacts.
- Verify the sender’s authenticity by contacting them through another channel before opening any attachments.
- Use reliable antivirus software and keep it updated with the latest definitions and patches.
- Enable multi-factor authentication for your Skype and other online accounts to prevent unauthorized access.
- Be wary of any messages that urge you to act quickly or offer too-good-to-be-true deals or rewards.
DarkGate is a dangerous malware that can compromise your system and data through Skype messages. By being vigilant and following the security tips above, you can protect yourself from this threat and enjoy a safe online communication experience.